ISO 27001 Certification55
ISO 27001 Certification
Introduction to ISO 27001 Certification
ISO 27001 certification is an internationally recognized standard focused on Information Security Management Systems (ISMS). It provides organizations with a systematic framework to identify, manage, and protect sensitive information from threats such as cyberattacks, data breaches, and unauthorized access. Achieving ISO 27001 certification demonstrates a strong commitment to information security, enhancing trust among customers, partners, and stakeholders while ensuring compliance with regulatory requirements.
Key Requirements of ISO 27001
The core requirements of ISO 27001 revolve around establishing, implementing, maintaining, and continually improving an effective ISMS. Organizations must begin with a risk assessment to identify potential security threats and vulnerabilities. Following this, appropriate risk treatment measures need to be implemented across physical, technical, and administrative controls. Additional requirements include creating information security policies, defining roles and responsibilities, ensuring staff training, implementing monitoring mechanisms, and conducting regular internal audits. These requirements help maintain a secure and compliant security environment.
Benefits of ISO 27001 Certification
ISO 27001 certification offers organizations multiple operational and strategic advantages. It builds customer confidence by proving that the organization takes data protection seriously. It also supports compliance with data protection laws such as GDPR and various national cybersecurity regulations. The certification helps minimize financial losses caused by security breaches, ensures business continuity by reducing disruptions, and enhances internal processes by promoting a risk-based approach. Additionally, ISO 27001 strengthens an organization’s competitive position by differentiating it as a security-conscious entity.
Steps to Achieve ISO 27001 Certification
The certification process typically begins with a gap analysis to understand the organization’s current security posture. After identifying gaps, the organization develops and implements an ISMS tailored to its context and risks. Documentation of policies, procedures, and controls plays a key role in this stage. Employees must be trained to understand their responsibilities in maintaining information security. Once the ISMS is implemented, an internal audit is performed to evaluate its effectiveness. This is followed by a certification audit conducted by an external certification body, which determines compliance with ISO 27001 requirements.
Conclusion
ISO 27001 certification is an essential milestone for organizations aiming to build a secure and resilient information management environment. By following structured security practices, addressing risks proactively, and demonstrating commitment to data protection, businesses not only safeguard their assets but also gain a significant competitive edge in the global market.
Categorias
Leia mais
The research field of targeted cancer therapies uses Imatinib Tablets IP 400 mg as a primary research component. Imatinib Tablets IP 400 mg function as a medical treatment for specific blood cancers and gastrointestinal tumors which medical professionals use. The tablets prevent cancer cells from receiving growth signals which faulty proteins produce to assist cancer patients. Doctors use...

In the modern corporate ecosystem, the traditional role of Human Resources has undergone a radical metamorphosis. No longer confined to filing paperwork and manual payroll processing, HR has evolved into "People Operations"—a data-driven department focused on employee experience, retention, and strategic growth. As we navigate through 2026, the catalyst behind this...

The market research for the global Tunnel Lighting market is an accumulation of first-hand facts and quantitative and qualitative evaluation and analysis for the forecast period (2024-2032). The report offers a comprehensive assessment of macro-economic indicators, parent market trends, and several factors influencing the market dynamics. In addition, it also assesses the latest...

Living on the beautiful Gold Coast offers stunning beaches, warm weather, and a relaxed lifestyle. However, the region’s subtropical climate also creates the perfect environment for many unwanted pests. From termites and ants to cockroaches and rodents, pests can quickly invade homes and businesses if not managed properly. This is why professional pest control services in Gold Coast are...

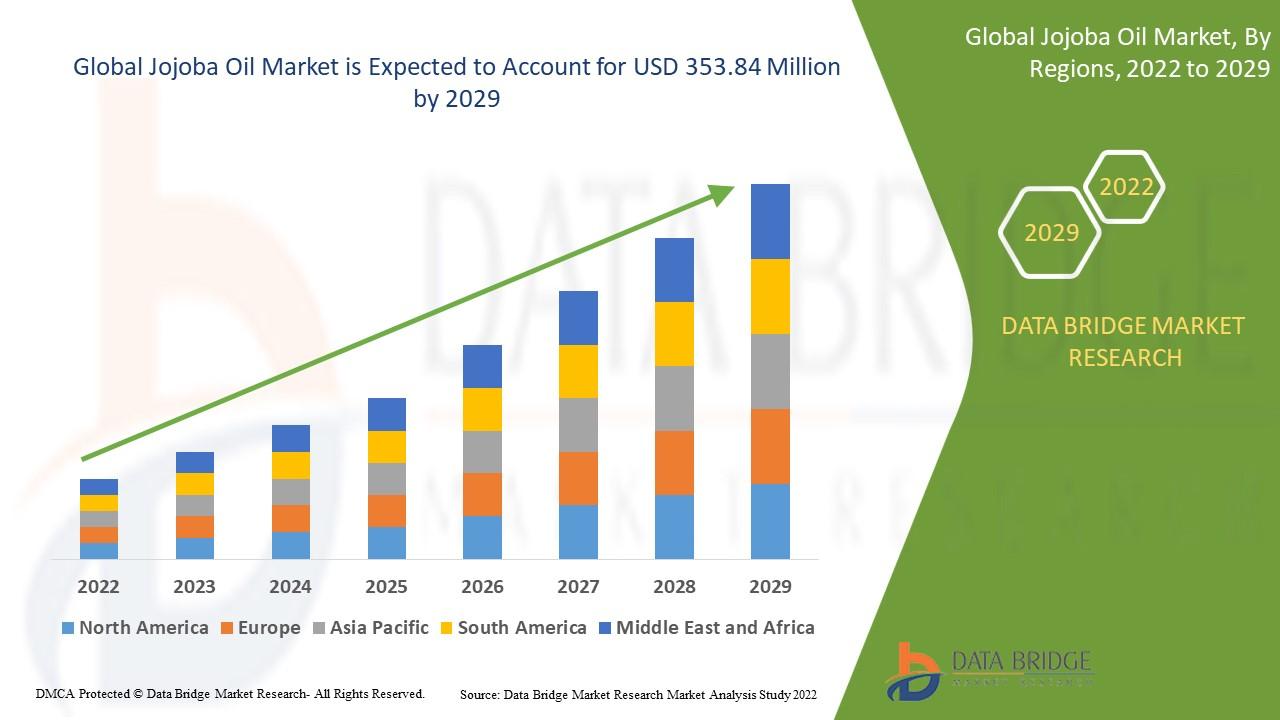
Jojoba Oil Market Report The Jojoba Oil Market is experiencing significant growth due to increasing demand in personal care, cosmetics, and pharmaceutical industries. This report provides a comprehensive analysis of market dynamics, trends, opportunities, and competitive strategies shaping the jojoba oil landscape globally. Market Overview Jojoba oil is a natural liquid wax derived...