How to Implement Findings from Penetration Testing

Cybra presents expert penetration testing services in Australia, covering Penetration Testing Melbourne, Penetration Testing Brisbane, and Penetration Testing Sydney, delivered by certified offensive-security professionals.
In today’s digital landscape, organizations in Melbourne are increasingly aware of the need to secure their information systems against cyber threats. As cyberattacks become more sophisticated, penetration testing has emerged as a vital tool for safeguarding sensitive data and maintaining customer trust.
What is Penetration Testing?
Penetration testing, often referred to as "pen testing," is a simulated cyberattack conducted to identify vulnerabilities in a system, network, or web application. The primary goal is to mimic the techniques used by malicious hackers to discover weaknesses that could be exploited. This proactive security measure helps organizations strengthen their defenses before a real attack occurs.
Why is Penetration Testing Essential?
-
Identifying Vulnerabilities: One of the core benefits of penetration testing is its ability to uncover potential security flaws. By identifying these weaknesses, organizations can address them proactively, thus reducing their risk exposure.
-
Regulatory Compliance: Many industries, including healthcare, finance, and e-commerce, are subject to strict regulatory requirements regarding data protection. Regular penetration testing can help organizations demonstrate compliance with standards such as PCI-DSS, HIPAA, and GDPR, avoiding hefty fines and reputational damage.
-
Risk Management: Understanding the vulnerabilities within an organization's infrastructure allows for informed risk management. By prioritizing issues based on their potential impact, businesses can allocate resources effectively to enhance their security posture.
-
Enhancing Security Awareness: Engaging in penetration testing not only identifies vulnerabilities but also raises awareness across the organization. Employees become more conscious of security threats and best practices, fostering a culture of security.
Types of Penetration Testing
Penetration testing can be categorized into several types, each focusing on different aspects of security:
-
External Penetration Testing: This tests the organization’s external-facing systems, such as web applications and servers, simulating attacks from outside the network.
-
Internal Penetration Testing: This type of testing evaluates the security of internal networks and systems, identifying vulnerabilities that could be exploited by an insider or an external attacker who has gained access.
-
Web Application Testing: Specialized testing that focuses on web applications to discover vulnerabilities like SQL injection, cross-site scripting (XSS), and improper authentication mechanisms.
-
Mobile Application Testing: As mobile apps become ubiquitous, this testing ensures that applications on mobile devices are secure against potential threats.
The Penetration Testing Process
The penetration testing process typically involves several phases:
-
Planning and Reconnaissance: Defining the scope of the test and gathering information about the target environment.
-
Scanning: Utilizing tools to identify live hosts, open ports, and services running on the systems.
-
Gaining Access: Attempting to exploit identified vulnerabilities to gain unauthorized access.
-
Maintaining Access: Evaluating whether the vulnerabilities can be exploited to maintain access within the system.
-
Analysis and Reporting: Documenting findings, providing recommendations for remediation, and presenting results to stakeholders.
Conclusion
For businesses in Melbourne, penetration testing is not just a security measure; it is a critical investment in their future. By identifying and addressing vulnerabilities through regular testing, organizations can fortify their defenses, comply with regulations, and foster a culture of security awareness. In a world where cyber threats are ever-present, penetration testing stands as a vital strategy to protect digital assets and maintain customer trust. Embracing this proactive approach can make all the difference in ensuring a resilient cybersecurity posture.
الأقسام
إقرأ المزيد
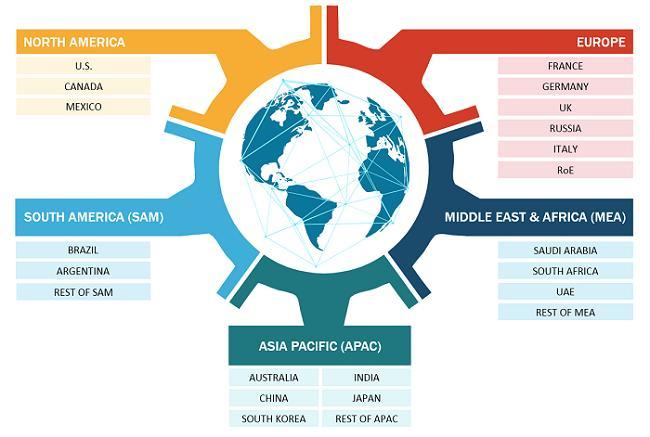
The global managed security services market was valued at USD 36.58 billion in 2024 and is expected to reach USD 90.31 billion by 2032During the forecast period of 2025 to 2032 the market is likely to grow at a CAGR of 11.96%, primarily driven by growing demand for advanced database security. The global business landscape is undergoing a transformation, with industries increasingly leaning on...

Die Welt der Einweg-Vapes entwickelt sich ständig weiter, und immer mehr Nutzer suchen nach Geräten, die sowohl eine hohe Leistung als auch ein komfortables Dampferlebnis bieten. Genau hier kommt der Fumot 12000 ins Spiel. Dieses moderne Gerät gehört zu den beliebtesten Optionen für Dampfer, die ein leistungsstarkes, langlebiges und gleichzeitig einfach zu nutzendes...

My mother was a beautiful woman inside and out. Tuesday afternoon, on the first day of trade show, around 180 menswear aficionados, and industry insiders paraded through the streets of Florence in their Sunday best. Fashion and beauty, at every level, will be a key tool in reframing stories and characters. Lawrence served up another mix matched ensemble we ca help but want to replicate. Playing...

The global flat steel market is entering a dynamic phase of transformation, driven by innovation in production processes, sustainability initiatives, and rising demand across diverse end-use industries. From infrastructure projects to automotive manufacturing, flat steel continues to be the backbone of modern industrial growth. This report provides a comprehensive analysis of the Flat Steel...
SEOHub: A Modern Approach to Digital Growth and Online Visibility Introduction to SEOHub SEOHub is a digital-focused concept designed to help websites improve their visibility on search engines and attract more organic traffic. In today’s competitive online environment, simply having a website is not enough. Businesses need structured strategies, consistent optimization, and data-driven...


