How to Implement Findings from Penetration Testing

Cybra presents expert penetration testing services in Australia, covering Penetration Testing Melbourne, Penetration Testing Brisbane, and Penetration Testing Sydney, delivered by certified offensive-security professionals.
In today’s digital landscape, organizations in Melbourne are increasingly aware of the need to secure their information systems against cyber threats. As cyberattacks become more sophisticated, penetration testing has emerged as a vital tool for safeguarding sensitive data and maintaining customer trust.
What is Penetration Testing?
Penetration testing, often referred to as "pen testing," is a simulated cyberattack conducted to identify vulnerabilities in a system, network, or web application. The primary goal is to mimic the techniques used by malicious hackers to discover weaknesses that could be exploited. This proactive security measure helps organizations strengthen their defenses before a real attack occurs.
Why is Penetration Testing Essential?
-
Identifying Vulnerabilities: One of the core benefits of penetration testing is its ability to uncover potential security flaws. By identifying these weaknesses, organizations can address them proactively, thus reducing their risk exposure.
-
Regulatory Compliance: Many industries, including healthcare, finance, and e-commerce, are subject to strict regulatory requirements regarding data protection. Regular penetration testing can help organizations demonstrate compliance with standards such as PCI-DSS, HIPAA, and GDPR, avoiding hefty fines and reputational damage.
-
Risk Management: Understanding the vulnerabilities within an organization's infrastructure allows for informed risk management. By prioritizing issues based on their potential impact, businesses can allocate resources effectively to enhance their security posture.
-
Enhancing Security Awareness: Engaging in penetration testing not only identifies vulnerabilities but also raises awareness across the organization. Employees become more conscious of security threats and best practices, fostering a culture of security.
Types of Penetration Testing
Penetration testing can be categorized into several types, each focusing on different aspects of security:
-
External Penetration Testing: This tests the organization’s external-facing systems, such as web applications and servers, simulating attacks from outside the network.
-
Internal Penetration Testing: This type of testing evaluates the security of internal networks and systems, identifying vulnerabilities that could be exploited by an insider or an external attacker who has gained access.
-
Web Application Testing: Specialized testing that focuses on web applications to discover vulnerabilities like SQL injection, cross-site scripting (XSS), and improper authentication mechanisms.
-
Mobile Application Testing: As mobile apps become ubiquitous, this testing ensures that applications on mobile devices are secure against potential threats.
The Penetration Testing Process
The penetration testing process typically involves several phases:
-
Planning and Reconnaissance: Defining the scope of the test and gathering information about the target environment.
-
Scanning: Utilizing tools to identify live hosts, open ports, and services running on the systems.
-
Gaining Access: Attempting to exploit identified vulnerabilities to gain unauthorized access.
-
Maintaining Access: Evaluating whether the vulnerabilities can be exploited to maintain access within the system.
-
Analysis and Reporting: Documenting findings, providing recommendations for remediation, and presenting results to stakeholders.
Conclusion
For businesses in Melbourne, penetration testing is not just a security measure; it is a critical investment in their future. By identifying and addressing vulnerabilities through regular testing, organizations can fortify their defenses, comply with regulations, and foster a culture of security awareness. In a world where cyber threats are ever-present, penetration testing stands as a vital strategy to protect digital assets and maintain customer trust. Embracing this proactive approach can make all the difference in ensuring a resilient cybersecurity posture.
Categorie
Leggi tutto
Resumen ejecutivo del informe de análisis del tamaño y la cuota de mercado de fundas y carcasas para móviles Data Bridge Market Research analiza que el mercado de fundas y carcasas para móviles se valoró en 20.550 millones de dólares en 2021 y se espera que alcance los 32.880 millones de dólares en 2029, registrando una CAGR...

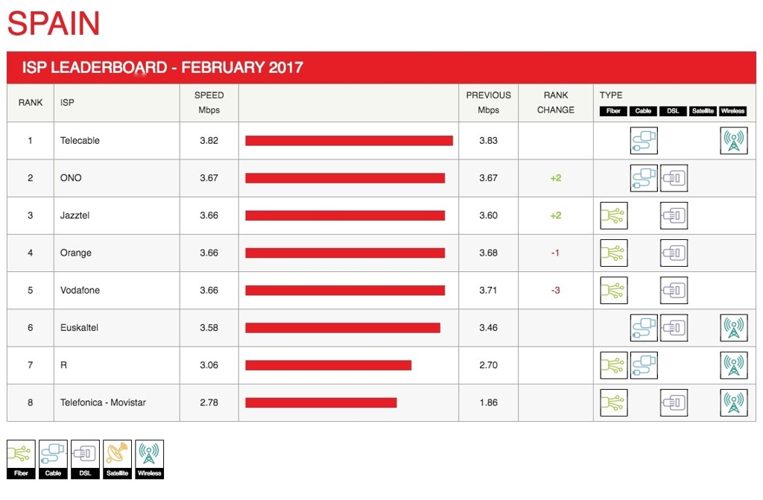
In February's Netflix ISP Speed Index, various global providers showed notable performance shifts. India's ACT broadband surged, climbing two positions to second place with a 0.41 Mbps increase. Airtel maintained its top rank in India, boosting its average speed to 2.58 Mbps. Spain's Telefónica Movistar recovered strongly, jumping 0.92 Mbps after a previous decline. This helped Spain...
Gallery Dept.: A Fusion of Art and Streetwear Gallery Dept. has emerged as one of the most distinctive names in contemporary streetwear, blending art, fashion, and culture into a single creative expression. Founded in Los Angeles, the brand quickly gained attention for its rebellious spirit and unconventional design philosophy. Rather than following mainstream fashion trends, Gallery...
Online communities have played a significant role in shaping modern sex dolls culture. As with many niche interests, the internet provides a space where individuals can share experiences, exchange knowledge, and connect without fear of judgment. These digital environments have helped transform what was once a private or stigmatized interest into a more openly discussed subject. Forums, social...

Efficient bathroom water management starts with a reliable Drain for Shower China that balances performance, durability, and visual appeal. These systems are designed to handle water effectively while maintaining a clean, minimalistic look, making them ideal for modern interiors. Properly engineered drains ensure smooth water flow, prevent pooling, and enhance overall hygiene, while their...


