How to Implement Findings from Penetration Testing

Cybra presents expert penetration testing services in Australia, covering Penetration Testing Melbourne, Penetration Testing Brisbane, and Penetration Testing Sydney, delivered by certified offensive-security professionals.
In today’s digital landscape, organizations in Melbourne are increasingly aware of the need to secure their information systems against cyber threats. As cyberattacks become more sophisticated, penetration testing has emerged as a vital tool for safeguarding sensitive data and maintaining customer trust.
What is Penetration Testing?
Penetration testing, often referred to as "pen testing," is a simulated cyberattack conducted to identify vulnerabilities in a system, network, or web application. The primary goal is to mimic the techniques used by malicious hackers to discover weaknesses that could be exploited. This proactive security measure helps organizations strengthen their defenses before a real attack occurs.
Why is Penetration Testing Essential?
-
Identifying Vulnerabilities: One of the core benefits of penetration testing is its ability to uncover potential security flaws. By identifying these weaknesses, organizations can address them proactively, thus reducing their risk exposure.
-
Regulatory Compliance: Many industries, including healthcare, finance, and e-commerce, are subject to strict regulatory requirements regarding data protection. Regular penetration testing can help organizations demonstrate compliance with standards such as PCI-DSS, HIPAA, and GDPR, avoiding hefty fines and reputational damage.
-
Risk Management: Understanding the vulnerabilities within an organization's infrastructure allows for informed risk management. By prioritizing issues based on their potential impact, businesses can allocate resources effectively to enhance their security posture.
-
Enhancing Security Awareness: Engaging in penetration testing not only identifies vulnerabilities but also raises awareness across the organization. Employees become more conscious of security threats and best practices, fostering a culture of security.
Types of Penetration Testing
Penetration testing can be categorized into several types, each focusing on different aspects of security:
-
External Penetration Testing: This tests the organization’s external-facing systems, such as web applications and servers, simulating attacks from outside the network.
-
Internal Penetration Testing: This type of testing evaluates the security of internal networks and systems, identifying vulnerabilities that could be exploited by an insider or an external attacker who has gained access.
-
Web Application Testing: Specialized testing that focuses on web applications to discover vulnerabilities like SQL injection, cross-site scripting (XSS), and improper authentication mechanisms.
-
Mobile Application Testing: As mobile apps become ubiquitous, this testing ensures that applications on mobile devices are secure against potential threats.
The Penetration Testing Process
The penetration testing process typically involves several phases:
-
Planning and Reconnaissance: Defining the scope of the test and gathering information about the target environment.
-
Scanning: Utilizing tools to identify live hosts, open ports, and services running on the systems.
-
Gaining Access: Attempting to exploit identified vulnerabilities to gain unauthorized access.
-
Maintaining Access: Evaluating whether the vulnerabilities can be exploited to maintain access within the system.
-
Analysis and Reporting: Documenting findings, providing recommendations for remediation, and presenting results to stakeholders.
Conclusion
For businesses in Melbourne, penetration testing is not just a security measure; it is a critical investment in their future. By identifying and addressing vulnerabilities through regular testing, organizations can fortify their defenses, comply with regulations, and foster a culture of security awareness. In a world where cyber threats are ever-present, penetration testing stands as a vital strategy to protect digital assets and maintain customer trust. Embracing this proactive approach can make all the difference in ensuring a resilient cybersecurity posture.
Nach Verein filtern
Read More
If you are looking for a refreshing escape from Dubai’s glamorous city life, the Hatta Tour is one of the most exciting and rewarding getaways you can choose. Surrounded by the majestic Hajar Mountains, Hatta offers a unique blend of cultural heritage, natural beauty, and adventurous activities. Whether you are a thrill-seeker, a culture lover, or simply in search of peace, this mountain...
The Smart Door Lock Market Size is witnessing rapid growth as consumers increasingly adopt smart home technologies to enhance security, convenience, and connectivity. The market was valued at USD 3.28 billion in 2025 and is projected to reach USD 21.85 billion by 2035, growing at a CAGR of 20.88% during the forecast period 2026–2035. Smart door locks are advanced security devices that...

The job market has changed significantly over the last decade. Businesses of every size now rely on digital platforms to reach customers, generate leads, and build brand awareness. As a result, digital marketing has become one of the most in-demand career paths for students, graduates, and working professionals looking to build future-ready skills. For those exploring a Digital Marketing Course...

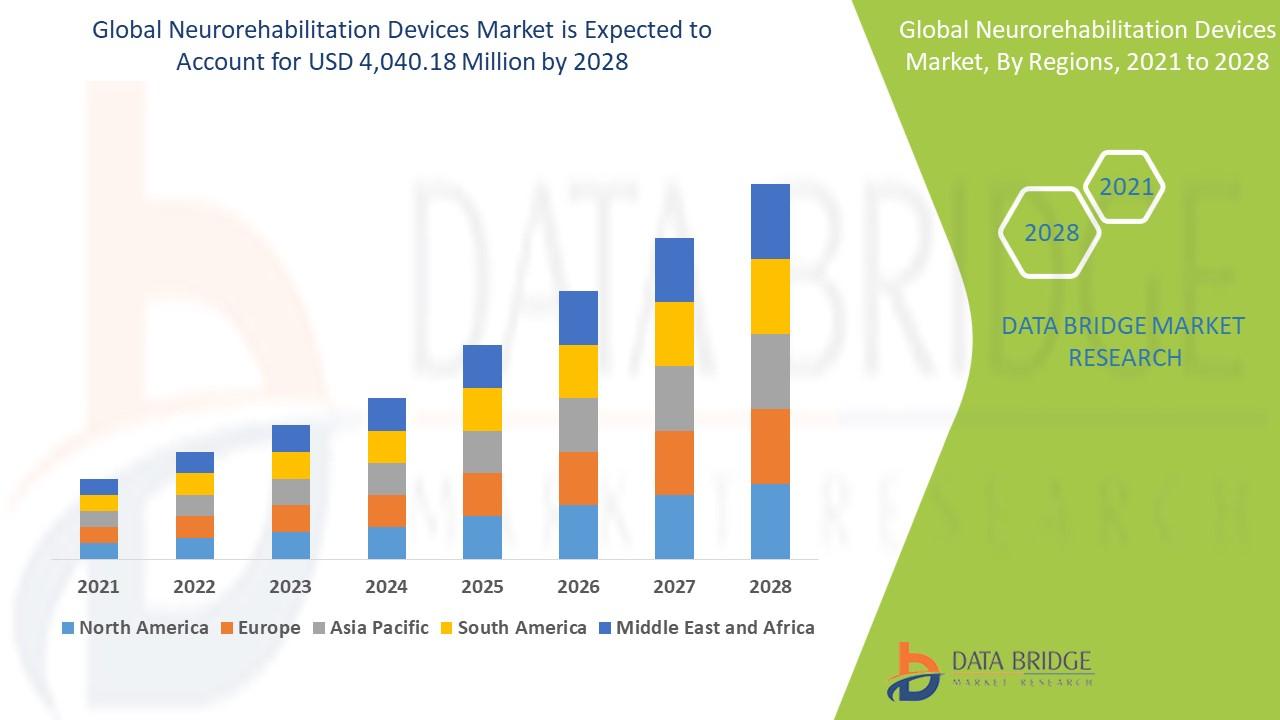
"Global Executive Summary Neurorehabilitation Devices Market: Size, Share, and Forecast CAGR Value Neurorehabilitation devices market is expected to gain market growth in the forecast period of 2021 to 2028. Data Bridge Market Research analyses the market to account to USD 4,040.18 million by 2028 and will grow at a CAGR of 13.12% in the above mentioned forecast period. Neurorehabilitation...
Managing a growing business requires constant attention to your technology infrastructure. Keeping hardware updated, securing sensitive data, and ensuring that employees have seamless access to their workstations can overwhelm internal IT teams. This is where outsourcing your workspace infrastructure becomes a strategic advantage. Understanding Managed Desktop Solutions Managed Desktop...


