How to Implement Findings from Penetration Testing

Cybra presents expert penetration testing services in Australia, covering Penetration Testing Melbourne, Penetration Testing Brisbane, and Penetration Testing Sydney, delivered by certified offensive-security professionals.
In today’s digital landscape, organizations in Melbourne are increasingly aware of the need to secure their information systems against cyber threats. As cyberattacks become more sophisticated, penetration testing has emerged as a vital tool for safeguarding sensitive data and maintaining customer trust.
What is Penetration Testing?
Penetration testing, often referred to as "pen testing," is a simulated cyberattack conducted to identify vulnerabilities in a system, network, or web application. The primary goal is to mimic the techniques used by malicious hackers to discover weaknesses that could be exploited. This proactive security measure helps organizations strengthen their defenses before a real attack occurs.
Why is Penetration Testing Essential?
-
Identifying Vulnerabilities: One of the core benefits of penetration testing is its ability to uncover potential security flaws. By identifying these weaknesses, organizations can address them proactively, thus reducing their risk exposure.
-
Regulatory Compliance: Many industries, including healthcare, finance, and e-commerce, are subject to strict regulatory requirements regarding data protection. Regular penetration testing can help organizations demonstrate compliance with standards such as PCI-DSS, HIPAA, and GDPR, avoiding hefty fines and reputational damage.
-
Risk Management: Understanding the vulnerabilities within an organization's infrastructure allows for informed risk management. By prioritizing issues based on their potential impact, businesses can allocate resources effectively to enhance their security posture.
-
Enhancing Security Awareness: Engaging in penetration testing not only identifies vulnerabilities but also raises awareness across the organization. Employees become more conscious of security threats and best practices, fostering a culture of security.
Types of Penetration Testing
Penetration testing can be categorized into several types, each focusing on different aspects of security:
-
External Penetration Testing: This tests the organization’s external-facing systems, such as web applications and servers, simulating attacks from outside the network.
-
Internal Penetration Testing: This type of testing evaluates the security of internal networks and systems, identifying vulnerabilities that could be exploited by an insider or an external attacker who has gained access.
-
Web Application Testing: Specialized testing that focuses on web applications to discover vulnerabilities like SQL injection, cross-site scripting (XSS), and improper authentication mechanisms.
-
Mobile Application Testing: As mobile apps become ubiquitous, this testing ensures that applications on mobile devices are secure against potential threats.
The Penetration Testing Process
The penetration testing process typically involves several phases:
-
Planning and Reconnaissance: Defining the scope of the test and gathering information about the target environment.
-
Scanning: Utilizing tools to identify live hosts, open ports, and services running on the systems.
-
Gaining Access: Attempting to exploit identified vulnerabilities to gain unauthorized access.
-
Maintaining Access: Evaluating whether the vulnerabilities can be exploited to maintain access within the system.
-
Analysis and Reporting: Documenting findings, providing recommendations for remediation, and presenting results to stakeholders.
Conclusion
For businesses in Melbourne, penetration testing is not just a security measure; it is a critical investment in their future. By identifying and addressing vulnerabilities through regular testing, organizations can fortify their defenses, comply with regulations, and foster a culture of security awareness. In a world where cyber threats are ever-present, penetration testing stands as a vital strategy to protect digital assets and maintain customer trust. Embracing this proactive approach can make all the difference in ensuring a resilient cybersecurity posture.
Categorias
Leia Mais
The world of food branding is the world where even a small detail can make a huge difference. The cone sleeve is one of the most ignored but strong constituents of food packaging. No matter how small or large your ice cream store or ice cream brand is, your cone sleeve is not merely a protective cover but a silent brand ambassador, even though you are not speaking directly. The cone sleeve on...

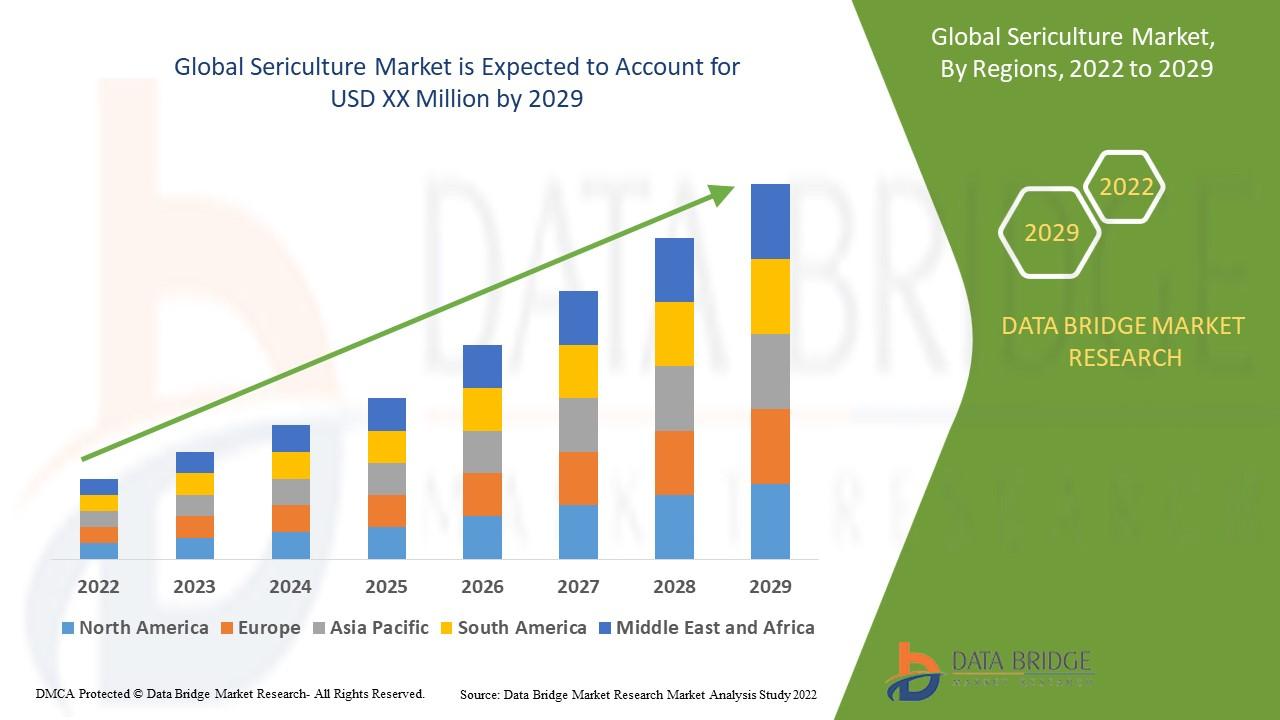
"Regional Overview of Executive Summary Sericulture Market by Size and Share CAGR Value The sericulture market is expected to witness market growth at a rate of 7.8% in the forecast period of 2022 to 2029. Data Bridge Market Research report on sericulture market provides analysis and insights regarding the various factors expected to be prevalent throughout the forecast period while...
Learn common mistakes while using a digital vernier caliper and improve accuracy with simple tips for better measurement results in daily work. Introduction A digital vernier caliper is one of the most useful measuring tools in workshops, factories, and even small DIY setups. It helps in measuring length, thickness, depth, and diameter with high accuracy. Many people prefer this...

成人向け漫画、いわゆる「エロ漫画」をインターネット上で楽しむ際、多くのユーザーが共通して抱えるストレスがあります。それは、画面の至る所に表示される不快な広告、クリックするたびにポップアップするリダイレクト画面、そして常に付きまとうセキュリティ上の不安です。せっかくお気に入りの作品に没頭しようとしても、画面を覆い尽くす下品なバナーや、ウイルス感染を警告する偽のポップアップによって、興奮や集中力が一瞬で冷めてしまったという経験は誰にでもあるのではないでしょうか。 こうしたユーザーの深刻な悩みに正面から応え、圧倒的な快適性と安全性を実現したのが、今大きな注目を集めているプラットフォーム「エロ漫画RAW」です。本記事では、なぜこのプラットフォームがこれほどまでに多くの読者から支持されているのか、その理由と魅力を徹底的に解き明かします。...

Cervicogenic headaches are a common yet often misunderstood type of headache that originates from problems in the cervical spine (neck). Unlike migraines or tension headaches, cervicogenic headaches are caused by issues such as poor posture, neck injuries, or spinal misalignment. If left untreated, they can significantly impact daily life, causing persistent pain that radiates from the neck to...


